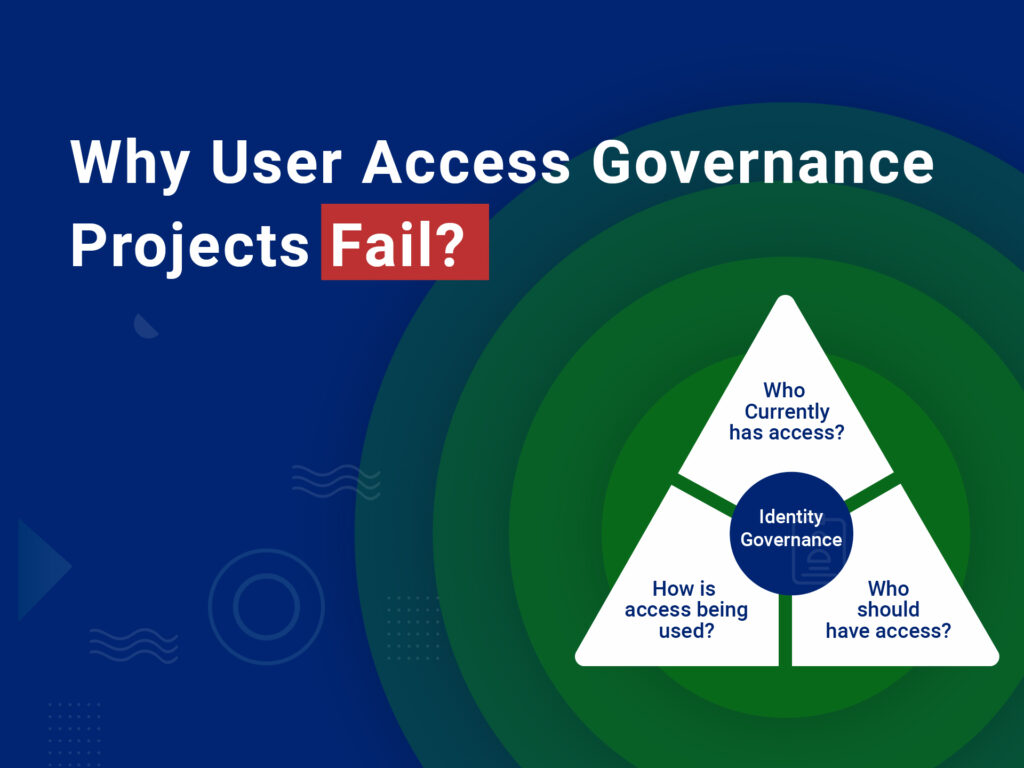
Companies are taking an “identity centric” view of IT controls and making investments to secure data and achieve compliance. However, not all investments are successful. Over the last few months, I have spoken with multiple industry leaders at conferences, interacted with prospects during demos, and worked closely with customers during implementations. Every so often I get to hear about failures security leaders had with implementing user access governance projects in their career. While the list of reasons for a particular project failure can vary, I do see a recurring theme across most botched implementations.
Complexity & Cost:
Today’s human or service identity sprawls across cloud, bring-your-own-devices (BYOD), BOT, etc. User identities exist in different forms within different systems and the user access governance solution has to synchronize these and provide a single identity for each business user. For example, procurement may have an expenses system that uses email address and password, and marketing may use active directory login credentials to authenticate users into their system. With these complex technological environments legacy, off-the-shelf solutions need extensive customization to accommodate today’s identity use cases. Projects are sold on the implementation prowess of the consulting team and grand vision. However, project teams go through a lengthy learning curve and undertake complex connector development work to deliver a fully integrated solution that provides a single pane of glass. This custom development results in prolonged project timelines and budget overruns. Once implemented, these customizations are difficult to troubleshoot and require constant intervention. Time and again we hear CFOs complain about the high Total Cost Of Ownership for the solution while CISOs bemoan the long-running service requests with consulting firms for these implementations.
Lack Of Adoption:
The success of any product relies on its unanimous adoption by end-users, and identity solutions are no exception. The solution should make life easier for users, not harder. Many product companies mistakenly believe product features and customer needs are the same. I don’t remember the last time I used many preset cycles on my washing machine? Identity products are not any different. Users hate cluttered interfaces and features which dazzle but rarely add any value. Many vendors in their haste to improve upon the Minimum Viable Product (MVP) extend the basic functions and end up with a product that does many things. The essential function gets lost. Unfortunately, this extensive functionality challenges end-users to memorize all the capabilities and features the platform provides. Inertia sets in, and the adoption stops. There is no dearth of examples where governance solution “went live” but was inevitably scrapped for the previous status quo, usually an Excel and Sharepoint solution.
It’s undeniable that any user access governance project carries a certain amount of risk. However, unless the product’s value is consistent with customer needs, it is bound to fail. Implementation processes and leading practices cannot make up for a product deficiency or in many cases feature bloat. The absolute key to success for organizations undertaking governance projects is to take a closer look at how “must-have” requirements tie with Total Cost Of Ownership and adoption. At SecurEnds we try to make a conscious decision to focus on both customer need and how customer’s recognize value.